Do you know your endpoints?
In 2025, endpoint threats are smarter, faster and can be more expensive than ever before. And they are one of the most vulnerable layers of attack. From laptops and phones to virtual machines and remote desktops, every endpoint is a potential entry point for malware, ransomware, or insider threats.
Endpoint Detection and Response (EDR) is a solid defense and is becoming the digital equivalent of locking your doors before going to sleep. It’s a smart security system that watches every device in real time, looking for signs of trouble and reacting immediately.
But EDR is of questionable value if it doesn’t have a complete inventory of which devices are out there, who’s using them, and how they are accessing your company’s data. That takes a cohort effort of modern tools: Microsoft Intune and Defender for Endpoints. When used together, you’ll have a more complete, secure endpoint strategy.
Let’s take a look at these tools and break it down.
Tip: If you’re still relying on legacy tools like SystemCenter Configuration Manager (SCCM), Microsoft’s legacy system for managing on-prem devices, you’re missing critical functionality in terms of endpoint visibility and response speed. SCCM wasn’t designed for a cloud-connected, mobile world.
Start with Intune: Foundation for Endpoint Visibility and Control
Modern endpoint security begins with modern endpoint management—and that means Microsoft Intune. As Microsoft phases out SCCM and encourages organizations to adopt Intune (or at least operate in a hybrid co-management state), the shift is more than a tooling update. It’s a shift toward mobility, identity-first security, and real-time defense.
Intune offers centralized management for all your endpoints—laptops, desktops, mobile devices, even BYOD hardware. It doesn’t just help you push policies or control updates. It establishes the baseline for identity and access management, compliance, and configuration.
Here’s what Microsoft Intune does:
Cloud-native management of Windows, iOS, Android, and macOS devices.
With Intune, you can configure, manage, and protect virtually any device from a single cloud-based console, no matter where that device is located. This reduces dependency on physical infrastructure and simplifies support for hybrid and remote workforces.
Built-in compliance and reporting tools to support regulatory requirements.
Intune can automatically verify if a device meets your organization’s security standards, such as encryption, OS version, or antivirus status. These compliance checks are logged and reportable, helping organizations demonstrate adherence to HIPAA, NIST, or other frameworks.
Seamless integration with Microsoft Defender for Endpoint to automate threat response.
When Defender (which we talk about later in this article) detects a threat, Intune can respond immediately by locking the device, forcing a restart, or revoking access. This built-in connection ensures rapid containment of attacks and reduces reliance on manual remediation.
Simplified deployment and reduced infrastructure needs compared to legacy SCCM setups.
Intune doesn’t require on-premises servers or VPN connections to deploy apps, updates, or policies. This drastically lowers setup costs, reduces maintenance overhead, and speeds up onboarding for new devices.
What Is Endpoint Detection and Response (EDR)?
Endpoint Detection and Response (EDR) is designed to close the gaps left by traditional antivirus tools. Microsoft’s Defender for Endpoint is one of the top-rated EDR platform, and both Gartner and Forrester are positioning Microsoft as a leader in the security space. In fact, Microsoft claims Endpoint blocked more than 9.6 billion malware threats in 2023 alone.
Here’s how EDR works differently than traditional tools:
- Real-time monitoring: It monitors the activity on every device for anomalies
- Behavioral analysis: Ituses machine learning to figure out when something doesn’t look right and builds a behavioral baseline for devices and flags deviations in context.
- Automated response: It automatically analyzes alerts using AI to determine whether an incident is real and what action is required.
- Automated Isolation: It isolates infected devices, blocks malicious files, and rolls back changes, often before a human analyst even begins their investigation.
- Cross-Platform Coverage: It works across multiple operating systems, including mobile, so you don’t need different tools to protect Windows, macOS, Linux, Android, and iOS.
How Intune and Defender Work Together
| Microsoft Intune | Defender: Endpoint Detection & Response (EDR) | |
| Main Purpose | Device management and policy enforcement | Threat detection and response |
| What it Manages | Device settings, app deployment, compliance rules | Security events, suspicious activity, active threats |
| Typical Use | Ensure only trusted, compliant devices access resources | Detect and contain cyberattacks in real time |
| Key Actions | Enroll devices, apply policies, block noncompliant access | Monitor behavior, isolate compromised devices |
EDR and Intune: The Case for Zero Trust
EDR and Intune are powerful parts of a broader picture. To fully secure your environment, you need to combine it with a Zero Trust strategy.
Zero Trust means:
- Never automatically trust a device or user, even if they’re inside your network
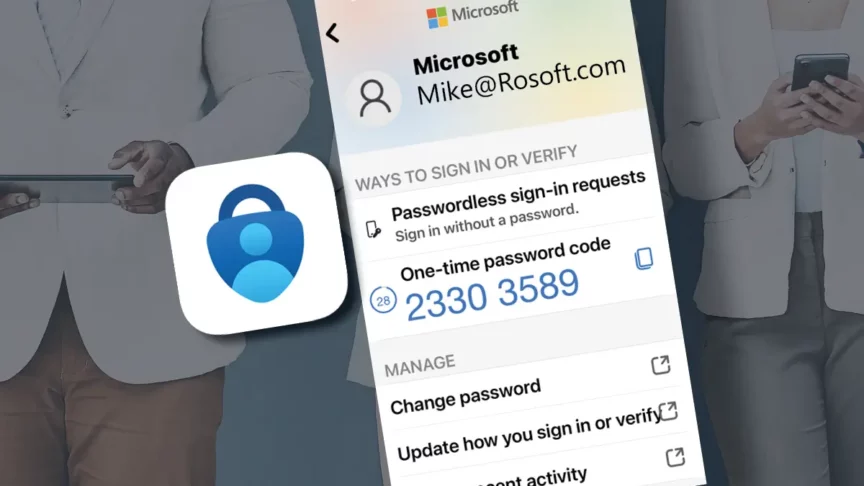
Zero Trust assumes that any user or device could be compromised, so access must always be earned—not given by default. This prevents lateral movement within the network and reduces the blast radius of a breach. - Always verify identity, device health, and risk level before granting access
Tools like Entra ID and Defender assess whether a login request is coming from a healthy, compliant device and a verified user. If any of those checks fail, access is denied or restricted, even if the password is correct. - Continuously monitor and enforce policies throughout a user session. If a device suddenly installs risky software or is flagged by Defender, its access can be revoked in real time.
When implemented it ensures that only the people, devices and processes that have been granted access to resources can use them. In short, if your devices aren’t enrolled in Intune, your EDR visibility is incomplete—and your Zero Trust journey is stalled.
JourneyTeam’s Zero Trust Security Assessment is designed to provide a clear, actionable strategy for strengthening your organization’s Microsoft 365 security posture. Tailored for businesses navigating modern cyber threats, our assessment helps IT and security leaders to adopt a Zero Trust architecture using the full capabilities of Microsoft tools.
How to Build a Modern Endpoint Security Strategy
Modern endpoint security isn’t just about installing antivirus and hoping for the best. IT teams need a strategy that covers the full lifecycle—managing devices, enforcing policies, detecting threats in real time, and responding automatically when something goes wrong.
The steps below outline a practical roadmap any security or IT team can follow to strengthen endpoint protection and stay ahead of evolving threats.
- Adopt Intune for Device Management: Move from SCCM to Intune (or use co-management) and enroll all laptops and mobile devices to enforce encryption, updates, and app restrictions.
- Enable Microsoft Defender for Endpoint: Turn on Defender (if included in your M365 license). Connect it to Intune, and ensure devices are sending telemetry for real-time threat detection. Tip: This can be enabled in passive mode which will provide you with insights even prior to enabling protection.
- Embrace Zero Trust Principles: Use Entra ID conditional access to enforce compliance and require MFA when risk is detected—don’t rely on location or VPN alone.
- Automate Incident Response: Leverage Defender’s automated investigation and response (AIR) to isolate compromised devices and alert IT without waiting for manual action.
- Monitor, Report, Improve: Review security dashboards regularly to spot non-compliance trends and adapt policies to new attack patterns.
This is a great starter list for how you can move from a patchwork of point solutions to a unified security posture. The result is fewer blind spots, faster incident response, and stronger protection for users and data without adding unnecessary complexity.
Need to Evaluate Your Endpoint Security Setup?
JourneyTeam has the security experts that can help you assess your endpoints and implement a security solution that makes your endpoints the new network perimeter, so you can prevent risks and detect suspicious activity no matter where employees are or the devices they are using to connect.
Schedule a Zero Trust Readiness Assessment with JourneyTeam to uncover gaps, prioritize actions, and align your defenses with the demands of 2025. As a Microsoft Solutions Partner for Security, you can rest assured you’ll have a partner who has the commitment to training and accreditation and has delivered solutions that lead to customer success. Let’s start a conversation!